Imagine that you are in one of the following situations:
- You have forgotten your password to connect to the personal workspace of your computer, and you want to reset it.
- After a wrong manipulation, you can not access the personal data of your computer, and you want to retrieve this access.
- You found a computer without supervision for which you are not the owner, but you want to see the file system’s content.
With a bootable USB key on Ubuntu, you can resolve these situations by first mounting the file system of the targeted computer with all permissions, then changing the password of any local user, and finally by connecting to the targeted workspace and exploring the file system.
First, plug your USB drive into the target computer and select your key as the boot device. This will enable the target computer to boot into the Ubuntu system on your USB drive. On a DELL computer, press F12 to access this selection. This information is visible on the welcome screen of your computer’s manufacturer.

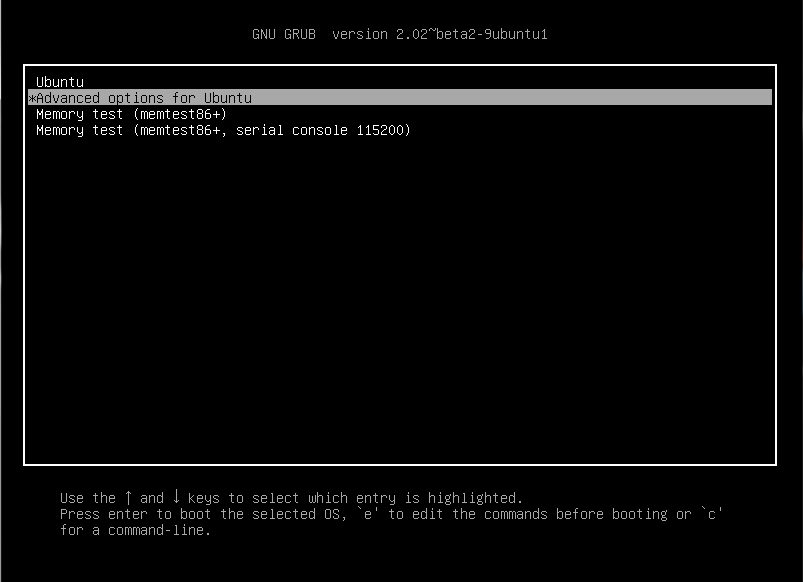
Start by choosing the following option:
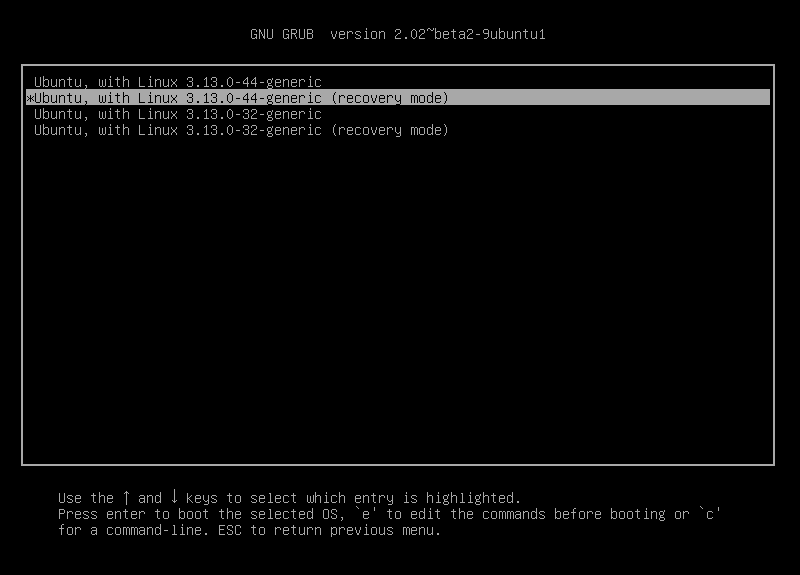
Then select the recovery mode:
Launch a root shell:
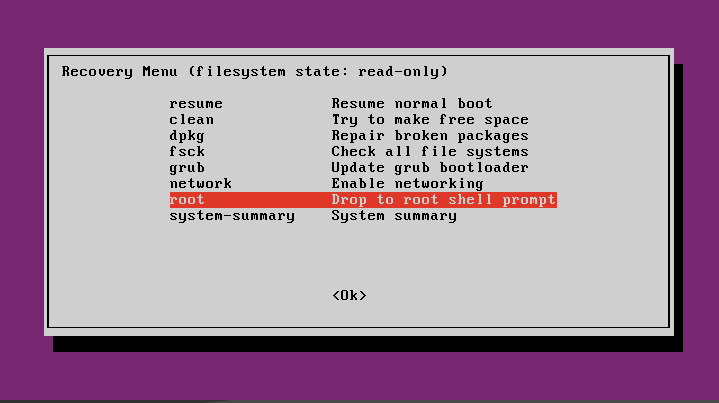
You access a device as a root user.
For the moment, the file system is only in read only, type the following command to mount the file system in read / write at the root of your key:
mount -o remount, rw /
Now you can copy the file system to an external hard drive, and then you can choose the new user password by typing:
passwd <username>
Type in the new password and confirm.
You can shut down the computer.
shutdown -h now
You can now turn on the computer normally and log in with the chosen user and password.
Well done ![]() !
!




Comments